Table of Contents
Understanding Application Security Fundamentals
In our increasingly digitized world, where applications are the backbone of technological advancements, ensuring their security is paramount. From personal banking to social media interactions, applications store, process, and transmit vast amounts of sensitive data. Understanding the fundamentals of application security is not just a necessity but a proactive measure in safeguarding against potential cyber threats.
The Core Concepts of Application Security
1. Authentication and Authorization: Authentication verifies the identity of users, ensuring they are who they claim to be. It involves mechanisms like passwords, biometrics, or multi-factor authentication. Authorization, on the other hand, determines what actions authenticated users are allowed to perform within the application. Implementing strong authentication and precise authorization rules is crucial for preventing unauthorized access.
2. Data Encryption: Data encryption involves converting data into a code to prevent unauthorized access. By encrypting data both in transit and at rest, even if intercepted, it remains unreadable without the encryption key. Employing robust encryption algorithms safeguards sensitive information from being compromised.
3. Input Validation: Input validation is the process of inspecting data entered into an application to ensure it conforms to specified formats and ranges. By validating inputs, applications can mitigate risks such as SQL injection and cross-site scripting attacks, which exploit vulnerabilities arising from unchecked user inputs.
4. Secure Coding Practices: Developers play a pivotal role in application security. Adhering to secure coding practices such as input sanitization, proper error handling, and avoiding hardcoded credentials strengthens the application’s resilience against exploitation. Regular code reviews and security audits help identify and rectify vulnerabilities early in the development lifecycle.
5. Security Patch Management: Software vulnerabilities are inevitable, but timely patching can significantly reduce the window of exploitation. Establishing robust patch management processes ensures that applications are promptly updated with the latest security patches and fixes, thereby mitigating the risk of known vulnerabilities being exploited.
Implementing a Comprehensive Security Strategy
1. Threat Modeling: Understanding potential threats and their impact is the cornerstone of an effective security strategy. Through threat modeling, organizations can identify, prioritize, and address security risks early in the development process, fostering a proactive approach to security.
2. Security Testing: Regular security testing, including penetration testing and vulnerability assessments, is essential for uncovering weaknesses in the application’s defenses. By simulating real-world attack scenarios, organizations can evaluate their security posture and remediate identified vulnerabilities before they are exploited maliciously.
3. Security Awareness Training: Human error remains one of the weakest links in application security. Educating employees and stakeholders about security best practices, common attack vectors, and the importance of adhering to security policies fosters a culture of security awareness throughout the organization.
Implementing Strong Authentication Measures

In today’s digital age, where data breaches and cyber threats are rampant, implementing strong authentication measures has become imperative for businesses and individuals alike. With the increasing sophistication of cybercriminals, traditional username and password combinations are no longer sufficient to protect sensitive information. Therefore, organizations must adopt advanced authentication methods to safeguard their assets and ensure data integrity.
Strong authentication, also known as multi-factor authentication (MFA) or two-factor authentication (2FA), adds an extra layer of security by requiring users to provide multiple forms of verification before granting access to a system or account. This additional layer of protection significantly reduces the risk of unauthorized access, as even if one factor is compromised, the others remain intact.
One of the most common forms of strong authentication is biometric authentication, which utilizes unique biological characteristics such as fingerprints, iris patterns, or facial recognition to verify a user’s identity. Biometric authentication offers a high level of security as these traits are difficult to replicate or steal, providing a more reliable means of authentication compared to traditional methods.
Another effective method is the use of hardware tokens or smart cards, which generate one-time passcodes that are synchronized with the authentication server. These tokens provide an additional level of security, as they are not susceptible to phishing attacks or password theft. Users must possess the physical token or card to authenticate their identity, adding an extra layer of protection against unauthorized access.
Additionally, SMS-based authentication and authenticator apps are widely used for 2FA, where users receive a temporary code via text message or generate codes through a mobile app. While these methods are convenient and easy to implement, they may be vulnerable to SIM swapping or device theft, highlighting the importance of combining them with other authentication factors for enhanced security.
Implementing strong authentication measures requires careful planning and consideration of various factors such as user experience, scalability, and regulatory compliance. Organizations must assess their security needs and choose authentication methods that best suit their requirements while balancing usability and security.
Furthermore, educating users about the importance of strong authentication and providing clear instructions on how to use these methods effectively is crucial for successful implementation. Training programs and awareness campaigns can help users understand the significance of protecting their accounts and the role they play in maintaining overall cybersecurity.
Securing Data Transmission: Encryption Techniques
In today’s digital era, where data is the currency of the realm, ensuring its secure transmission has become paramount. With cyber threats lurking at every corner of the internet, employing robust encryption techniques is crucial to safeguard sensitive information from prying eyes. Let’s delve into the world of encryption and explore the techniques that fortify data transmission against potential breaches.
Understanding Encryption:
At its core, encryption is the process of encoding data in such a way that only authorized parties can access and decipher it. It involves transforming plaintext into ciphertext using algorithms and cryptographic keys, rendering the information unintelligible to unauthorized entities.
Key Encryption Techniques:
- Symmetric Encryption: Symmetric encryption employs a single key for both encryption and decryption processes. This key is shared between the sender and the recipient, ensuring secure communication. Popular symmetric encryption algorithms include AES (Advanced Encryption Standard) and DES (Data Encryption Standard).
- Asymmetric Encryption: Asymmetric encryption, also known as public-key encryption, utilizes a pair of keys: public and private. The public key is used for encryption, while the private key is kept secret and used for decryption. This technique facilitates secure communication over untrusted networks and is widely used in digital signatures and secure email communication. RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography) are common asymmetric encryption algorithms.
- Hash Functions: Hash functions are cryptographic algorithms that transform data into a fixed-size string of characters, known as a hash value or digest. Unlike encryption, hash functions are irreversible, meaning the original data cannot be retrieved from the hash value. Hash functions play a crucial role in data integrity verification and password storage.
- Transport Layer Security (TLS): TLS, the successor of SSL (Secure Sockets Layer), is a cryptographic protocol that ensures secure communication over a computer network. It encrypts data transmitted between clients and servers, preventing eavesdropping and tampering. TLS employs symmetric and asymmetric encryption techniques for key exchange and data encryption, providing a robust security layer for web applications, email servers, and other network services.
Best Practices for Data Transmission Security:
- Strong Encryption Algorithms: Utilize industry-standard encryption algorithms like AES with sufficiently long keys to enhance security.
- Key Management: Implement robust key management practices, including key generation, distribution, rotation, and storage, to prevent unauthorized access.
- End-to-End Encryption (E2EE): Employ end-to-end encryption to protect data throughout its entire journey, from sender to recipient, without intermediary access.
- Regular Updates and Patches: Stay updated with the latest security patches and updates for encryption software and protocols to mitigate vulnerabilities and exploits.
- Multi-factor Authentication (MFA): Combine encryption with MFA mechanisms like biometrics or one-time passwords to add an extra layer of security against unauthorized access.
Protecting Against Injection Attacks: SQL, XSS, and Beyond

In today’s digitally interconnected world, the threat of injection attacks looms large over individuals and organizations alike. These attacks, including SQL injection (SQLi) and Cross-Site Scripting (XSS), pose significant risks to the security and integrity of data and systems. As cybercriminals continuously evolve their techniques, it’s crucial for individuals and businesses to understand these threats and implement robust measures to protect against them.
Understanding Injection Attacks
Injection attacks exploit vulnerabilities in software applications that allow malicious code to be injected into legitimate commands or queries. Among the most common types are SQL injection and Cross-Site Scripting.
- SQL Injection (SQLi): In SQL injection attacks, malicious actors insert malicious SQL code into input fields of a web application. If these inputs are not properly validated or sanitized, attackers can manipulate the SQL queries executed by the application’s database, potentially gaining unauthorized access to sensitive data, modifying or deleting records, or even taking control of the entire database.
- Cross-Site Scripting (XSS): XSS attacks involve injecting malicious scripts into web pages viewed by other users. These scripts can steal session cookies, deface websites, redirect users to malicious sites, or perform other malicious actions on behalf of the attacker.
Protecting Against Injection Attacks
Preventing injection attacks requires a multi-layered approach involving both secure coding practices and the use of specialized security mechanisms. Here are some effective strategies:
- Input Validation and Sanitization: Implement strict input validation and sanitization routines to ensure that all user-supplied data is properly formatted and does not contain any malicious code. This includes validating input types, length, and format, as well as sanitizing input to remove potentially harmful characters.
- Parameterized Queries: Use parameterized queries or prepared statements in database access code to separate SQL logic from data. By passing parameters separately from the SQL query, you can prevent malicious input from altering the query structure.
- Escaping Output: Escape user-generated content before displaying it in web pages to prevent XSS attacks. This involves encoding special characters such as <, >, and & to their HTML entities, ensuring that they are treated as plain text rather than executable code.
- Content Security Policy (CSP): Implement a Content Security Policy to mitigate the risk of XSS attacks by specifying the trusted sources of content that the browser should execute or render. CSP can help detect and mitigate XSS attempts by restricting the execution of scripts and other potentially harmful content.
- Firewalls and Intrusion Detection Systems (IDS): Deploy web application firewalls (WAFs) and intrusion detection systems (IDS) to monitor and filter incoming traffic for suspicious patterns indicative of injection attacks. These systems can help block malicious requests before they reach the application, providing an additional layer of defense.
- Regular Security Audits and Penetration Testing: Conduct regular security audits and penetration testing to identify and address potential vulnerabilities in your applications. By proactively assessing your systems for weaknesses, you can stay one step ahead of attackers and fortify your defenses accordingly.
Proper Input Validation: Guarding Against Vulnerabilities
In the realm of cybersecurity, the adage “better safe than sorry” couldn’t be more relevant. One of the fundamental pillars of fortifying digital systems against malicious attacks is proper input validation. This often overlooked yet critical process acts as a formidable barrier against vulnerabilities that could compromise the integrity and security of your applications and databases. Let’s delve into why proper input validation is paramount in safeguarding your digital assets.
Understanding Input Validation
At its core, input validation is the process of scrutinizing and validating data input to ensure that it conforms to the expected format, type, and range. Whether it’s user inputs in web forms, API requests, or data from external sources, every piece of incoming data must undergo thorough scrutiny. By enforcing strict validation rules, you can mitigate the risks associated with various cyber threats such as SQL injection, cross-site scripting (XSS), and command injection.
Guarding Against Vulnerabilities
The significance of input validation becomes apparent when considering the myriad of vulnerabilities that can exploit lax validation protocols. Let’s take a closer look at some of the most common threats and how proper input validation acts as a robust defense mechanism:
1. SQL Injection (SQLi): SQL injection attacks occur when malicious actors inject malicious SQL queries into input fields, exploiting vulnerabilities in the application’s database layer. By employing robust input validation techniques such as parameterized queries and input sanitization, developers can thwart SQL injection attempts, preventing unauthorized access to sensitive data.
2. Cross-Site Scripting (XSS): Cross-Site Scripting attacks involve injecting malicious scripts into web pages viewed by other users. Proper input validation, coupled with output encoding, can effectively neutralize XSS threats by sanitizing user inputs and ensuring that any potentially dangerous content is neutralized before rendering.
3. Command Injection: Command injection attacks exploit vulnerabilities in applications that dynamically construct system commands using user-supplied inputs. By implementing stringent input validation measures, developers can prevent malicious actors from executing arbitrary commands on the underlying system, thereby averting potential security breaches.
Best Practices for Effective Input Validation
To bolster your defense against cyber threats, consider implementing the following best practices for robust input validation:
- Use Whitelisting: Define strict validation rules that only accept inputs matching predefined criteria, thereby rejecting any inputs that deviate from the expected format or type.
- Sanitize Inputs: Employ input sanitization techniques to remove or neutralize any potentially malicious content, such as HTML tags, special characters, and escape sequences.
- Implement Server-Side Validation: Never rely solely on client-side validation as it can be bypassed. Perform thorough validation checks on the server-side to ensure the integrity and security of incoming data.
- Regularly Update Validation Rules: Stay vigilant and update your validation rules regularly to adapt to evolving cyber threats and emerging attack vectors.
- Utilize Frameworks and Libraries: Leverage reputable frameworks and libraries that offer built-in input validation functionalities, saving time and ensuring consistency across your applications.
Regular Security Audits and Penetration Testing

In today’s interconnected digital landscape, where data breaches and cyber threats loom large, safeguarding sensitive information has become paramount for businesses of all sizes. With cyberattacks evolving in sophistication and frequency, relying solely on traditional security measures is no longer sufficient. This is where regular security audits and penetration testing step in as crucial pillars of defense, helping organizations fortify their digital fortresses against potential breaches.
Understanding Security Audits and Penetration Testing
Security audits involve a comprehensive review of an organization’s security protocols, systems, and policies. They aim to identify vulnerabilities, assess risks, and ensure compliance with industry regulations and best practices. These audits may encompass various aspects such as network security, application security, physical security, and data protection measures.
Penetration testing, on the other hand, is a proactive approach to security assessment. Also known as ethical hacking, it involves simulating real-world cyberattacks to uncover weaknesses in an organization’s defenses. By mimicking the tactics of malicious hackers, penetration testers attempt to exploit vulnerabilities and assess the effectiveness of existing security controls.
The Importance of Regular Audits and Testing
- Identifying Vulnerabilities: Cyber threats are constantly evolving, and new vulnerabilities emerge regularly. Regular security audits and penetration testing help organizations stay ahead of these threats by identifying weaknesses in their systems and infrastructure before malicious actors can exploit them.
- Enhancing Security Posture: By proactively identifying and addressing security gaps, organizations can strengthen their overall security posture. This proactive approach reduces the likelihood of successful cyberattacks and minimizes the potential impact of security breaches.
- Ensuring Compliance: Many industries are subject to stringent regulatory requirements regarding data protection and cybersecurity. Regular security audits help organizations ensure compliance with these regulations, avoiding costly fines and legal consequences associated with non-compliance.
- Protecting Sensitive Data: Data breaches can have severe consequences, including financial losses, reputational damage, and legal liabilities. Regular audits and penetration testing help organizations identify and address vulnerabilities that could compromise the confidentiality, integrity, and availability of sensitive data.
- Building Customer Trust: In today’s digital economy, trust is a valuable currency. Demonstrating a commitment to cybersecurity through regular audits and testing can enhance customer trust and loyalty. By safeguarding their data against potential threats, organizations can instill confidence in their customers and differentiate themselves from competitors.
Best Practices for Effective Audits and Testing
- Define Clear Objectives: Clearly define the scope and objectives of each security audit and penetration testing exercise to ensure thorough coverage and meaningful results.
- Engage Qualified Professionals: Security audits and penetration testing require specialized knowledge and expertise. Engage qualified cybersecurity professionals or reputable third-party vendors with proven track records in conducting these assessments.
- Regularly Update Security Measures: Cyber threats evolve rapidly, making it essential to continuously update security measures to address emerging risks. Regular audits and testing help organizations identify areas where security controls may need enhancement or modification.
- Implement Remediation Plans: Upon identifying vulnerabilities or weaknesses, develop and implement remediation plans to address them promptly. Regularly review and update these plans to ensure ongoing effectiveness.
- Educate Staff: Human error remains one of the most significant cybersecurity risks. Provide regular training and awareness programs to educate employees about security best practices and the importance of vigilance in safeguarding sensitive information.
Managing User Permissions and Access Controls
In today’s digital landscape, the management of user permissions and access controls stands as a pivotal aspect of cybersecurity and data governance. With the exponential growth of digital assets and the increasing complexity of organizational structures, ensuring that the right individuals have the appropriate level of access to sensitive information is paramount. In this guide, we delve into the intricacies of managing user permissions and access controls, offering insights and strategies to fortify your organization’s security posture.
Understanding User Permissions and Access Controls
User permissions refer to the rights granted to individuals or groups within an organization, dictating what actions they can perform and what resources they can access. Access controls, on the other hand, are the mechanisms through which these permissions are enforced, typically implemented through authentication, authorization, and auditing processes.
Importance of Effective Management
Effective management of user permissions and access controls is crucial for several reasons:
- Data Security: Unauthorized access to sensitive data can lead to data breaches, financial losses, and reputational damage.
- Compliance: Many industries are subject to regulatory requirements mandating strict control over access to certain types of information (e.g., healthcare data under HIPAA).
- Operational Efficiency: Granting appropriate access rights streamlines workflows and ensures that users have the resources they need to perform their roles efficiently.
Best Practices for Managing User Permissions and Access Controls
1. Role-Based Access Control (RBAC): Implementing RBAC involves defining roles within the organization and assigning permissions to these roles rather than individual users. This approach simplifies management and ensures consistency across the organization.
2. Principle of Least Privilege (PoLP): Adhering to the principle of least privilege involves granting users only the permissions necessary to perform their tasks, minimizing the potential impact of a compromised account.
3. Regular Reviews and Audits: Periodically reviewing user permissions and access controls is essential to ensure that they align with organizational needs and that no unnecessary privileges have been granted over time. Auditing logs can help identify any unauthorized access attempts or suspicious activities.
4. Multi-Factor Authentication (MFA): Implementing MFA adds an extra layer of security by requiring users to provide multiple forms of authentication, such as a password and a one-time code sent to their mobile device, reducing the risk of unauthorized access due to compromised credentials.
5. Employee Training and Awareness: Educating employees about the importance of data security and their role in maintaining it is paramount. Regular training sessions can help raise awareness about best practices, such as the importance of safeguarding login credentials and reporting suspicious activities.
Leveraging Technology Solutions
Several technology solutions are available to assist organizations in managing user permissions and access controls:
- Identity and Access Management (IAM) Platforms: IAM platforms centralize user authentication and authorization processes, providing administrators with granular control over user access rights.
- Privileged Access Management (PAM) Solutions: PAM solutions focus on managing and securing privileged accounts, which have elevated permissions and pose a higher risk if compromised.
- Security Information and Event Management (SIEM) Systems: SIEM systems aggregate and analyze log data from various sources to detect and respond to security incidents in real-time.
Keeping Software Dependencies Up-to-Date
In the ever-evolving landscape of technology, software dependencies play a crucial role in ensuring the functionality, security, and performance of applications. From operating systems to libraries and frameworks, modern software relies on a multitude of dependencies to operate efficiently. However, one aspect that often gets overlooked is the importance of keeping these dependencies up-to-date. In this guide, we delve into the significance of staying current with software dependencies and explore best practices to maintain a healthy and secure software ecosystem.
Understanding Software Dependencies:
Before delving into the importance of updating software dependencies, let’s grasp what they are. Software dependencies are external libraries, modules, or frameworks that an application relies on to function correctly. These dependencies often include code written by third-party developers and are integrated into the application to provide additional functionality or streamline development processes.
The Importance of Keeping Software Dependencies Updated:
1. Security Vulnerabilities: Outdated software dependencies are a breeding ground for security vulnerabilities. Hackers continuously exploit known vulnerabilities to compromise systems and steal sensitive data. By keeping dependencies up-to-date, developers can mitigate these risks by patching known vulnerabilities and ensuring that their applications are protected against potential security threats.
2. Performance Enhancements: Software updates often include performance enhancements and optimizations that can significantly improve the speed and efficiency of an application. By staying current with software dependencies, developers can leverage these enhancements to deliver a seamless user experience and stay ahead of the competition.
3. Compatibility: As technology evolves, software dependencies may become incompatible with newer versions of operating systems, frameworks, or libraries. By keeping dependencies up-to-date, developers can ensure compatibility with the latest technologies and prevent compatibility issues that may arise from using outdated software components.
4. Bug Fixes: Like any software, dependencies are prone to bugs and glitches that can affect the stability and functionality of an application. Regular updates often include bug fixes and patches that address these issues, providing developers with a more reliable and robust software ecosystem.
Best Practices for Keeping Software Dependencies Up-to-Date:
1. Automated Dependency Management: Utilize automated dependency management tools and services to streamline the process of updating software dependencies. Tools like package managers and dependency checkers can automatically detect outdated dependencies and suggest updates, reducing the manual effort required to keep dependencies current.
2. Regular Maintenance: Incorporate regular dependency maintenance into your development workflow. Schedule periodic reviews of software dependencies and prioritize updates based on the severity of security vulnerabilities, performance improvements, and bug fixes.
3. Dependency Versioning: Adopt a versioning strategy for managing software dependencies. By tracking the version numbers of dependencies used in an application, developers can easily identify outdated components and assess the impact of updating to newer versions.
4. Security Monitoring: Implement continuous security monitoring to detect and mitigate security vulnerabilities in software dependencies. Utilize vulnerability scanning tools and services to identify potential threats and take proactive measures to secure your software ecosystem.
5. Community Support: Engage with the developer community and leverage their expertise to stay informed about updates and best practices for managing software dependencies. Participate in forums, mailing lists, and online communities dedicated to software development to stay ahead of emerging trends and technologies.
Monitoring and Logging for Early Threat Detection
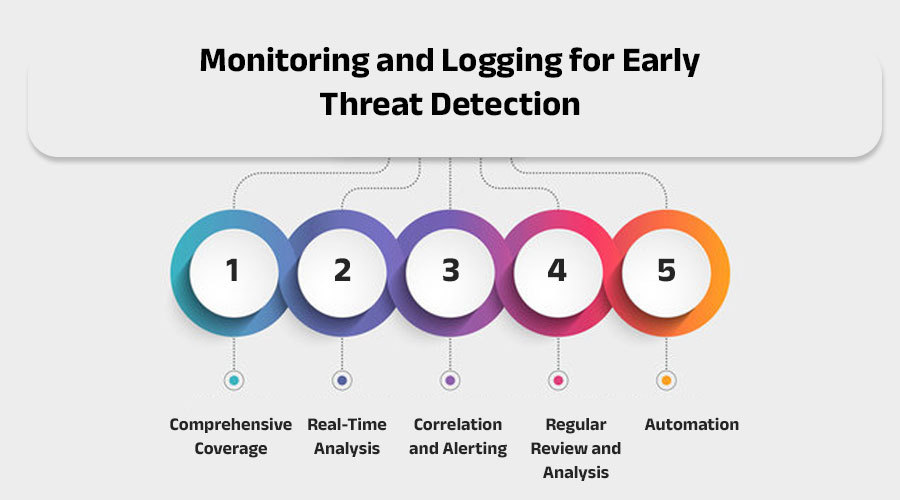
In today’s interconnected digital landscape, cybersecurity is paramount. As cyber threats become increasingly sophisticated, organizations must adopt proactive measures to safeguard their systems and data. One such measure is the implementation of robust monitoring and logging practices for early threat detection.
Monitoring and logging play a pivotal role in cybersecurity by providing real-time visibility into network activities and identifying potential security incidents before they escalate into full-blown breaches. By continuously monitoring system events, administrators can detect anomalies, unauthorized access attempts, and other suspicious activities that may indicate a security threat.
The process begins with the deployment of monitoring tools that capture and analyze various types of data, including network traffic, system logs, and user activity. These tools use advanced algorithms and machine learning techniques to identify patterns and deviations from normal behavior, allowing security teams to swiftly respond to potential threats.
Logging, on the other hand, involves the systematic recording of events and activities within an IT environment. This includes everything from user logins and file modifications to system configurations and application usage. By maintaining detailed logs, organizations can reconstruct events leading up to a security incident and conduct thorough forensic investigations if necessary.
To maximize the effectiveness of monitoring and logging, organizations should adhere to several best practices:
- Comprehensive Coverage: Monitor all critical assets, including servers, endpoints, and network devices, to ensure complete visibility into the IT infrastructure.
- Real-Time Analysis: Implement real-time analysis capabilities to quickly identify and respond to security threats as they occur, minimizing the potential impact of an attack.
- Correlation and Alerting: Utilize correlation engines to correlate data from multiple sources and generate actionable alerts based on predefined rules and thresholds.
- Regular Review and Analysis: Regularly review logs and monitor alerts to identify emerging threats and fine-tune detection capabilities based on evolving attack patterns.
- Automation: Leverage automation to streamline the monitoring and response process, enabling faster detection and remediation of security incidents.
By investing in monitoring and logging solutions, organizations can strengthen their cybersecurity posture and mitigate the risk of data breaches and other cyber threats. Early threat detection not only helps prevent financial losses and reputational damage but also ensures the integrity and confidentiality of sensitive information.
Top Application Security and Secure App Development Companies
In today’s digitized landscape, where technology has woven itself into the fabric of our lives, the security of applications stands as a paramount concern. With cyber threats looming large, individuals and organizations alike are increasingly turning to specialized firms for fortifying their digital assets. Let’s delve into the realm of application security and explore the top companies spearheading the charge towards safer digital ecosystems.
-
-
Next Big Technology:

Focus Area
- Mobile App Development
- App Designing (UI/UX)
- Software Development
- Web Development
- AR & VR Development
- Big Data & BI
- Cloud Computing Services
- DevOps
- E-commerce Development
Industries Focus
- Art, Entertainment & Music
- Business Services
- Consumer Products
- Designing
- Education
- Financial & Payments
- Gaming
- Government
- Healthcare & Medical
- Hospitality
- Information Technology
- Legal & Compliance
- Manufacturing
- Media
-
- Checkmarx: Pioneering the field of static application security testing (SAST), Checkmarx provides cutting-edge solutions for identifying and remediating security vulnerabilities in software code. Their platform seamlessly integrates with development environments, enabling developers to secure their applications without disrupting workflow.
- Synopsys: As a leader in software integrity, Synopsys delivers comprehensive solutions for building secure, high-quality software. From static analysis to software composition analysis and beyond, Synopsys equips organizations with the tools and expertise needed to mitigate security risks across the software development lifecycle.
- IBM Security: Leveraging the power of artificial intelligence and machine learning, IBM Security offers a suite of application security solutions designed to protect businesses from evolving cyber threats. With offerings ranging from application security testing to runtime application self-protection, IBM Security empowers organizations to stay one step ahead of attackers.
- Micro Focus: With a focus on modernizing application security, Micro Focus provides solutions that help organizations build security into every stage of the software development lifecycle. Their comprehensive suite of tools encompasses static analysis, dynamic analysis, and interactive application security testing, ensuring thorough protection against security vulnerabilities.
- Rapid7: Recognized for its innovative approach to application security, Rapid7 offers solutions that combine advanced analytics with automation to help organizations identify and prioritize security risks effectively. From web application scanning to container security, Rapid7 equips businesses with the tools needed to secure their digital assets in today’s dynamic threat landscape.
- Fortify: A division of Micro Focus, Fortify specializes in providing application security solutions that enable organizations to build secure software at scale. With offerings for static application security testing, dynamic application security testing, and secure coding education, Fortify empowers businesses to deliver resilient applications in an ever-changing world.
- WhiteHat Security: Focused on empowering DevSecOps teams, WhiteHat Security offers a cloud-based platform for securing web applications at scale. By combining static application security testing with dynamic application security testing and human expertise, WhiteHat Security helps organizations identify and remediate security vulnerabilities before they can be exploited by attackers.
- Acunetix: A leading provider of automated web application security solutions, Acunetix offers a comprehensive suite of tools for scanning, detecting, and remedying security vulnerabilities in web applications. With features such as vulnerability prioritization and integration with popular issue trackers, Acunetix helps organizations streamline their application security efforts.
- Contrast Security: Renowned for its next-generation application security platform, Contrast Security delivers real-time, continuous protection for web applications and APIs. By embedding security directly into the application runtime, Contrast Security enables organizations to detect and block attacks in real-time, without sacrificing performance or scalability.
FAQs On Application Security and Secure App Development
In today’s digital age, ensuring application security is paramount for businesses and individuals alike. With the proliferation of cyber threats, understanding the ins and outs of secure app development is crucial. Here, we delve into frequently asked questions (FAQs) surrounding application security to provide clarity and guidance on building robust and resilient applications.
- What is Application Security? Application security refers to the measures taken throughout the application’s lifecycle to protect it from threats and vulnerabilities. It encompasses various practices, including code reviews, penetration testing, encryption, and access control, aimed at safeguarding the confidentiality, integrity, and availability of data and resources.
- Why is Application Security Important? In today’s interconnected world, applications store and process sensitive information, making them prime targets for cyber attacks. A breach in application security can lead to data theft, financial losses, reputational damage, and legal liabilities. By prioritizing application security, organizations can mitigate these risks and build trust with their users.
- What are the Common Threats to Application Security? Common threats to application security include SQL injection, cross-site scripting (XSS), cross-site request forgery (CSRF), insecure authentication, and insufficient logging and monitoring. These vulnerabilities can be exploited by attackers to gain unauthorized access, manipulate data, or disrupt services.
- How Can Developers Ensure Secure App Development? Developers can ensure secure app development by following best practices throughout the software development lifecycle. This includes conducting thorough security assessments, implementing secure coding practices, regularly updating dependencies, and integrating security testing into the development process. Additionally, fostering a security-conscious culture within the development team is essential for maintaining vigilance against emerging threats.
- What Role Does DevSecOps Play in Application Security? DevSecOps, an extension of DevOps practices, integrates security into every stage of the software development lifecycle. By automating security testing, incorporating security controls into infrastructure as code, and promoting collaboration between development, operations, and security teams, DevSecOps enables organizations to deliver secure and resilient applications at scale.
- How Can Organizations Ensure Compliance with Regulatory Standards? Many industries are subject to regulatory standards governing data privacy and security, such as GDPR, HIPAA, PCI DSS, and SOC 2. Organizations can ensure compliance with these standards by implementing appropriate security controls, conducting regular audits, and staying abreast of regulatory updates. Engaging with legal and compliance experts can also provide guidance on meeting regulatory requirements.
- What Steps Should I Take in Response to a Security Incident? In the event of a security incident, swift and decisive action is essential to minimize damage and restore trust. This may involve containing the breach, conducting forensic analysis to determine the scope and impact of the incident, notifying affected parties, and implementing remediation measures to prevent future occurrences. Additionally, organizations should communicate transparently with stakeholders and regulators to demonstrate accountability and commitment to security.
Thanks for reading our post “Application Security 7 Ways to Build a More Secure App”. Please connect with us to learn more about Best Application Security.








